In the fast-evolving field of cybersecurity, staying ahead of emerging threats requires a comprehensive understanding of your own infrastructure. As an example, subdomain enumeration is an important step in the reconnaissance phase of the attacker lifecycle. Of the many tools available for subdomain enumeration, Anubis is one of the easiest to use while maintaining efficiency and reliable results. T This article will discuss how Anubis works and the key features of the tool, along with providing a use case to demonstrate how it all works in real life.
Anubis
Anubis is an open-source enumeration tool that automates the enumeration of subdomains for any given domain. It is very useful for penetration testers, security analysts, and system administrators who need to identify hidden and/or forgotten subdomains for possible attack vectors.
Some key advantages of Anubis include:
- Easy to Use: It has a minimalistic design and allows for quick results.
- Efficient: It uses multiple APIs and search engines to provide a breadth of results.
- Automated: It can do much of the enumeration automatically, reducing the manual aspect.
Anubis gathers data from several data sources, including search engine advertisements, certificate transparency logs, and public APIs, to create a comprehensive view of the subdomains.
Why Subdomain Enumeration Matters
Subdomain enumeration is a fundamental aspect of reconnaissance in cybersecurity. Many organizations suffer from improperly configured websites, often due to an unmaintained existence of web applications, APIs, and other services being hosted on their subdomains.
As a result, the unmonitored subdomains can become vulnerability entry points for an attacker. By identifying subdomains much earlier – and more accurately – they provide management and security teams a way to mitigate the risks of:
- Exposed Development Environments: such as the test server, test environment, or development instance that was never intended to go live.
- Misconfigured Subdomains: such as subdomains that have been configured to insecure settings or entirely unprotected.
- Takeover Vulnerabilities: such as subdomains that point to a resource that no longer exists or is deprecated (unmanaged domains), opening them up for completely arbitrary takeover.
This tool is intended to assist in the subdomain enumeration of a website or web application. It can be difficult to identify subdomains hosted on HTTPS sites or web applications; however, the tool wraps the find subdomains for both an HTTP/HTTPS site in a simple tool called Anubis, which is a Python tool – so once you’ve installed Python on your Kali Linux system, it is available for use.
The features that Anubis provides – the user interface itself -look very much like Metasploit 1 and later Metasploit 2, making it straightforward to use by utilizing the consistent design for an easy and user-friendly experience; thus, making it exceedingly easy for all tiers of security researchers to use the tool, and providing the tool with a user interface that is easy, straight forward, and usable.
Installation:
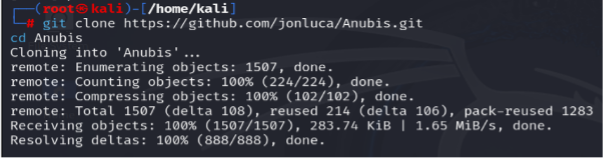
Step 1: To install the tool on your operating system, run the following command:
git clone https://github.com/jonluca/Anubis.git
Once the installation is complete, move into the tool’s directory by using:
cd Anubis
Step 2: After downloading and navigating to the directory, install the necessary dependencies by running:
pip3 install -r requirements.txt

The requirements have been installed. Now, we will see an example of how to use the tool.
Usage
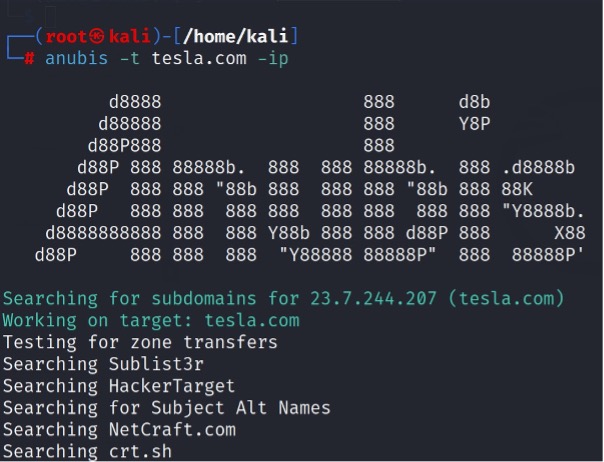
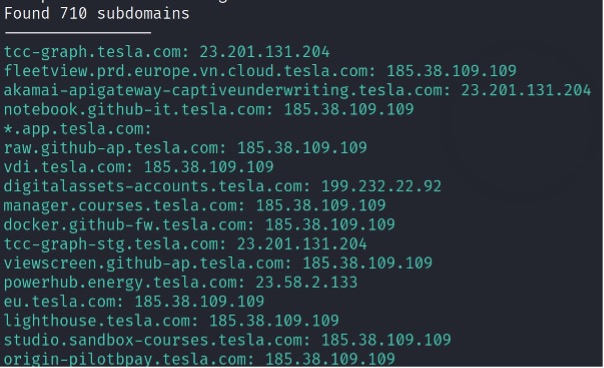
Find the subdomain of the domain tesla.com and its IP address.
Integrating Anubis into Workflow
Anubis can be integrated into broader reconnaissance workflows. For instance:
- Combine it with Nmap to scan discovered subdomains for open ports.
- Use it alongside tools like Shodan or Censys for in-depth analysis of subdomain services.
- Automate periodic scans with a cron job to monitor domain changes over time.
Limitations and Considerations:
While Anubis is a powerful tool, it has certain limitations:
- Rate Limits: Some APIs may throttle queries if usage limits are exceeded.
- Coverage: No tool can guarantee 100% coverage; consider complementing Anubis with manual searches or other enumeration tools.
- False Positives: Verify results to eliminate outdated or incorrect entries.
To maximize its effectiveness:
- Keep the tool updated.
- Use API keys from supported services to expand query capabilities.
Conclusion
Anubis is a powerful and convenient subdomain enumeration and information-gathering tool. Automating and collecting data from multiple sources is a great addition to any security professional’s toolkit. With Anubis, security professionals can identify and remediate risks adjoining subdomains and improve their overall security posture.
To test Anubis today, start figuring out the hidden layers of your own infrastructure and better defend against possible attacks.





